What does a Penetration Tester Do?¶
Notes and links from the presentation are located on my Github [[https]]://github.com/theo2612
¶
Rea & Asssociates¶
What is a penteration Tester and what do they do?¶
Continuous Education¶
ME¶
I'm Brad Theodore but before I tell you about me and Pen Testing.¶
My Wife
Amy. She's a saint. They got a cloud waiting for her. She's seen me at my absolute best and worst and keeps me. Our family is one of the most inspiring forces in my life.

Our 2 kids. Dominic and Rosie
Dominic
He runs cross country and track and has almost lettered in both and has a 4.0 currently.

Rosie
She consumes books like I consume Reese's cups, quickly. She swims and plays soccer. Well not really play, she is an animal out there, not afraid of someone bigger than her. In fact, I'm pretty sure she looks for em. Yeah.

And me - I have a bachelors in Hospitality Management from YSU - I have a masters in Information Technology with a concentration in Cyber Security. I did a lot of academic paper reading and hands on work. but truth be told a lot of my actual hands on experience came after university. - I've worked in the Restaurant, Beverage and Trucking industries. I firmly believe that my time spent in those industries has prepared me for my career in Cyber Security. - I work for Rea and Associates as a Pen-Tester. - Who knows what a pen tester is ?
I'm a hacker? No a Pen Tester
Clicky tops

Twisty bottoms
And the zebra of the pen world the clippy clicker

Penetration Tester¶
No of course, I work for Rea and Associates as a Penetration Tester and I love what I do.
- It is one of the most frustrating and rewarding journeys I've embarked on. My company has clients, they point me at a target, computer, server or website and say get in there.
- We offer the following [[https]]://www.reacpa.com/service/cybersecurity/
- Information & Cybersecurity
- Policy Drafting
- Comprehensive GRC/Governance, Risk, Compliane Reporting
- Control Data Mapping
- SOC/NOC Advisory Services - Security Operation Center/Network Operations Center
- Vulnerability & Penetration Testing
- Physical Security Assessments
- Vendor Management/Third-Party Risk/Selection Assistance
- Data Discovery, Classification Exposure Monitoring.
- CyberSecurity Maturity Model Certification
- My Office - Rea computer, My Desktop, My Server

What hacking is not¶
- Blackhat [[https]]://youtu.be/zPd_LDsbZWM?t=16
- Swordfish bad [[https]]://youtu.be/RJ1Oqixk2mE?t=28
What hacking is¶
- Swordfish accurate
- Discord - social engineering
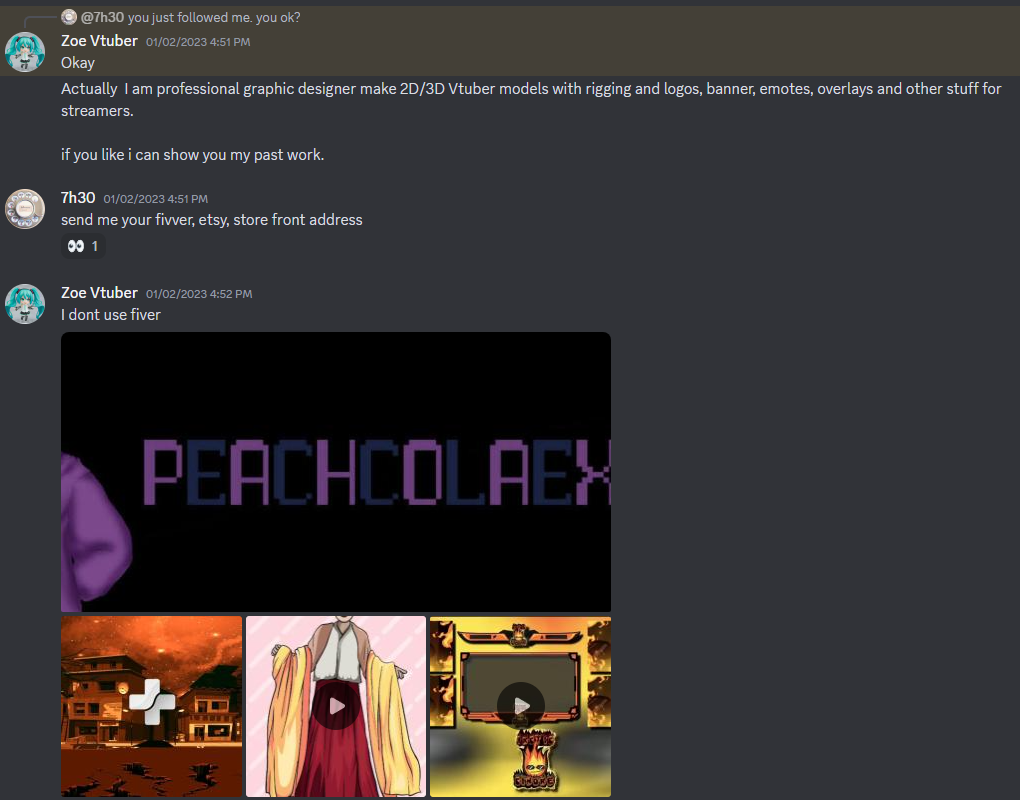
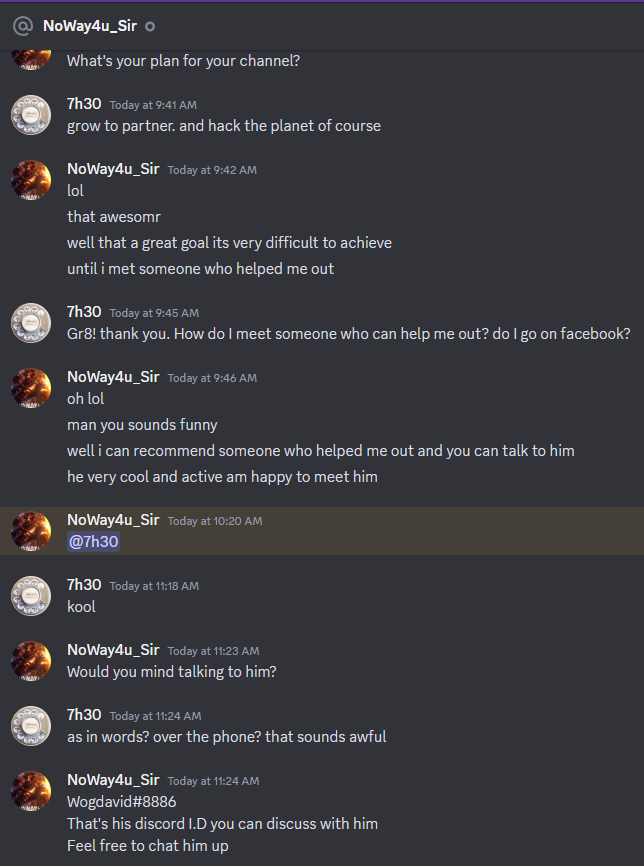
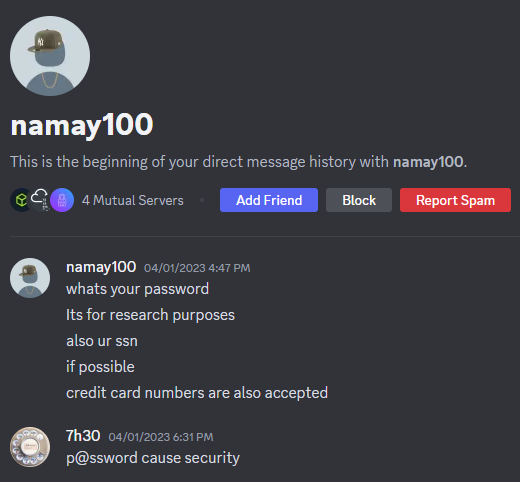 - Phishing - scam calls
- Phishing - scam calls
Engagements¶
Some engagements are easy and some not so much. - One was an external pentest of a website with bill pay. Through a [[dirbuster]] scan I found a wordpress login page exposed to the internet. While booting my [[password cracking]] software, I tried admin/admin, and that logged me in. I had access for a week no one booted me off the website, even while logging in and out multiple times. One of the times it asked me to confirm my contact email, which I could have changed. Also, with admin access to the wordpress site, I could have pointed the bill pay address to spoofed website and redirected payments. - Another time it was an all html website with a db that was meant to be open to the internet. I was diving through piles of CVE's hoping one was unpatched. a week later I still did not have access.
More Background about me¶
I compiled a list of my favorite platforms for continuous education.
Continuous Education / Resources¶
OWASP top 10 [[https]]://owasp.org/Top10/ Their Top 10 most critical CyberSecurity categories Most recent revision was 2021 where Broken Access Control jumped 4 spots to #1 OverTheWire [[https]]://overthewire.org/wargames/bandit/ Where I started - took me about a year to complete Bandit Great beginner dive into [[linux]] and basic commands Website security, Cryptography, exploitation [[TryHackMe]] [[https]]://[[tryhackme]].com/ Great beginner dive into exploiting machines Great rooms for learning about exploits ExplainShell [[https]]://explainshell.com/ Spectacular resource for learning and explaining command line commands Professor Messer [[https]]://www.youtube.com/c/professormesser Excellent free and paid resource for certificate study TCM Security [[https]]://academy.tcm-sec.com/courses/ Economical resource for CyberSecurity OpenAI - ChatGPT – [[https]]://chat.openai.com I use constantly through my day Analyze code blocks What does this command do? How do I use nmap to scan for devices on my network? How do I use openAI's api to invoke chatGPT from the command line?
Advanced Exploit DB [[https]]://www.[[exploit-db]].com/[[searchsploit]] DB of CVE's [[searchsploit]] from command line Hacktricks [[https]]://book.hacktricks.xyz/welcome/readme giant repo for exploits [[HackTheBox]] [[https]]://www.[[hackthebox]].com/ more realistic machines to exploit "easy" boxes are not always easy shodan [[https]]://www.shodan.io/ search engine for intenet connected devices
Pentester Best Practices Patience Resiliance Adaptation Self Teaching / Self Learning / continuous education [[https]]://[[tryhackme]].com/room/outlookntlmleak Collaboration - help others Less experienced to encourage Same experience for accountability More experience for mentorship Note taking CherryTree, notion, obsidian, word ... whatever you use. Take notes.
What should you be doing additionally? create
Easy Github Blogs LinkedIN
Hard Podcasts – USB our Guest Twitch – PainfulIT YouTube